Bitcoin Fraud: types, schemes, security rules

Content
The cryptocurrency environment is actively scaling and attracting new enthusiasts. However, new members of the crypto community are often at risk of hacker attacks due to their inexperience, which negatively affects their further desire to dive into the crypto world. On the one hand, Bitcoin gives freedom to humanity, but on the other hand, its open philosophy presents unscrupulous users with the opportunity to profit in dishonest ways.
To prevent you from being among those who lost their Bitcoins due to scammers, we have prepared an overview of the most common fraudulent schemes. Armed with this information, you can avoid Bitcoin scams and deny cybercriminals the chance to get hold of your coins.
Fake crypto exchanges
Where does the potential owner of cryptocurrencies go? Of course, to the crypto exchange. This is really the right decision since modern exchangers make it easy not only to buy Bitcoin but also to understand the basic trading routine. However, when entering “crypto-exchange”, “buy Bitcoin” and other keywords into the search engine, you should always be careful because the search results’ first lines may contain fake exchanges. The sites of such exchanges are as similar as possible to popular and honest services, but these are their fraudulent copies.
In addition to websites, you may come across fake applications, the purpose of which is to gain access to your funds.
Most often, unscrupulous copies promise the lowest commissions, give out generous gifts and even impressive amounts of cryptocurrency for registration and trading. Firstly, remember that the more fabulous the offer sounds, the more likely you are to pay double the price. Secondly, if this is your first time deciding to register on the exchange, enter its address manually and add it to your bookmarks.
Also, don’t follow the links that may be sent to you via messengers, even if the link is very similar to the correct one. Fake exchanges are often hosted under similar addresses with minimal changes that are difficult to spot.
For example, to register on the WhiteBIT exchange, enter the address whitebit.com. There should not be any other letters, numbers, or symbols in it.
Suspicious giveaways
We have already mentioned above that scammers really like to lure their victims with promises. Fake giveaways are no exception. If you see an announcement that you can get a big reward for a small contribution, immediately close all links. This scheme is quite old and simple, but for some reason, it is still in demand: the victim sends funds to someone else’s address and waits for more coins to arrive. But it’s not difficult to guess that by transferring your Bitcoins, you are giving them to a scammer with no hope of getting anything in return.
Of course, any popular cryptocurrency can participate in this scheme. Moreover, there are times when the scammers’ target is your private keys or other important information.
Fake giveaways can be found on social networks or in comments to posts of popular projects. In order not to fall for the deceivers’ bait, just don’t participate in such promotions, where you need to send funds to receive a prize.
Extortion
One of the most morally cruel frauds is extortion. Victims are deprived of their funds and subjected to intense psychological pressure.
Scammers send threats to reveal sensitive information of victims if they are not receiving a ransom. By the way, this information can often be fake, but strong pressure from attackers forces you to send BTC to their addresses.
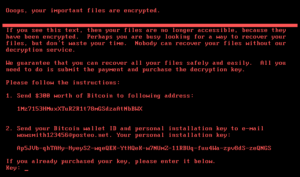
Everyone remembers the massive hacker attack called Petya, which disabled thousands of devices around the world. The ransomware blocked access to all files stored on the computer and demanded a ransom in Bitcoins to decrypt and restore access to the data.
Scammers don’t sleep and continue to improve this type of ransomware viruses. To keep yourself and your devices safe, install an antivirus and don’t forget about regular updates. Don’t click on advertising and suspicious links, and pay special attention to files you receive via email.
Also, set up regular backups to restore files in case of virus damage.
Follow the basic rules of online behavior: don’t provide your personal information to suspicious services and online stores, try not to sync your social media accounts with various sites, and don’t forget about two-factor authentication.
If scammers have chosen you as their victim, carefully check the information they want to use for blackmail. If the information isn’t true, ignore the pesky hackers.
Phishing
In one of our articles, we examined the problem of phishing attacks in detail. But we can’t fail to mention it when the topic of Bitcoin scams is concerned.
Most often, we are faced with phishing on social networks. Fraudsters copy the pages of popular personalities and announce giveaways on their pages. Therefore, check all sources and page indicators that may indicate authenticity (check marks, number of real subscribers, dates of first publications, etc.).
Among the phishing schemes, it’s also necessary to highlight fraud using emails.
The letters often contain a call to protect the accounts or download some files. At the same time, the sender’s address will not raise any suspicions, because it will look like an official letter.
You need to be especially careful when potential intruders ask you to upload documents or reset your password. Basically, their purpose is to gain access to your accounts and wallets.
If the letter seems suspicious to you, explore its address, it should not contain errors in the company name and additional characters. Don’t hesitate to request information from the company from which the letter allegedly came. Contact its representatives through the official address indicated on the website.
Ponzi schemes and pyramids
Ponzi schemes and various pyramids have become classics of the crypto industry fraud.
The Ponzi scheme is a kind of investment strategy in which the income of early investors is paid out through the investments of new participants. When an unscrupulous project wants to hide, the site abruptly stops working, the creators delete their accounts in social networks, and investors are left without their money.
The pyramid, in turn, provides profit to those members who attract more new people.
The best way not to become one of the participants of such schemes is to choose the assets for investment carefully. Pay attention to the project’s tokenomics. If the influx of new investors provides the growth of the coin/token, you are in a pyramid or a Ponzi scheme.
P.S. — Unfortunately, fraudulent schemes will always be present on the market. But don’t let cybercriminals take over your cryptocurrency. Be one step ahead.